Research and Summary Notes
Scopenoes from ICTethics research at Cesagen, Lancaster University.
- Introductory note
Need for ethical reflection and understanding of morality presupposes conflict and requires dedication to questions of who is in conflict and whose values are at stake. Much less attention is devoted to the question of what the ethics ought to be ethics of. For example, ethics of technology tend to take the technology in question at face value, even if it does not (and may never) exist except in scenarios of an uncertain future.
See our Summary Note on the ethical aspects of advanced ICTs
and the compiled reference list from ICTethics research at Cesagen.Also, our summarised Policy Views on:
eHealth technologies
Body modification
The internet of things
The burden of securityand our Scopenotes on Issues in Focus.
- Key lessons from development areas and flagship investigations
Cesagen has contributed ethical reflections that address all four ICTethics research domains (A - D). We have also been in charge of domain B, on the convergence of physical, mental and virtual phenomena, including flagship investigations into assistive robotics and "smart" implants.
See our Summary Note on key lessons from research domain B
and our Summary and Research Notes on each of the strategic development domains and research focus areas:Focus area: Personal health systems
B - Convergence of the physical, mental and virtual
Focus area: Assistive robotics and "smart" implants
Focus area: Radio-frequency identification (RFID)
Focus area: Biometric identification
-
The development of intelligent environments
The activities for which intelligent environments are conceived involve: eTraffic, airports, eHealth, hospitals, homes, schools, and ordinary workplaces. These environments are conceived on the assumption that embedded intelligence can reliably capture the identity and state of objects, persons, bodies and minds, and flawlessly process information in order to 'know' what to do next.
Key problems stem from the impossibilities of such seamlessness.
Focus area: Personal health systems
 Scenario exercises like Being Diabetic in 2011 (ENISA, 2009) foreground common
concerns about the dynamic recording of health conditions --issues regarding access,
mission creep, security, unintended consequences of interoperability and
risk relating to the (in)accuracy of data. The work of ENISA has also explored the
generational gap in sentiments about what counts as invasion of privacy or if/how the
dignity of persons is challenged with remote monitoring systems which are personalized
to assist the individual.
Scenario exercises like Being Diabetic in 2011 (ENISA, 2009) foreground common
concerns about the dynamic recording of health conditions --issues regarding access,
mission creep, security, unintended consequences of interoperability and
risk relating to the (in)accuracy of data. The work of ENISA has also explored the
generational gap in sentiments about what counts as invasion of privacy or if/how the
dignity of persons is challenged with remote monitoring systems which are personalized
to assist the individual.
Also prepared and delivered by Cesagen:
1) Gunnarsdóttir, K. and Arribas-Ayllon, M. (2010). Researching experience: Engineering `synergetic prosperity'. Presented at the EASST Biannual Conference in Trento, 2 Sep 2010.
2) Gunnarsdóttir, K. and Arribas-Ayllon, M. (2011, discussion paper). Ambient Intelligence: a narrative in search of users. Draft copy available at Lancaster University (Nov 2011).
-
The convergence of physical, mental and virtual
Convergence of physical, mental and virtual phenomena is primarily manifested in the development of assistive robotics, including advanced bionics and body/brain implant technologies. Convergence can be viewed in terms of degree or intensity. Latest developments in robotics are greatly concerned with the assistive potential which largely rests on advanced mobility, sensory and monitoring capabilities. But physically and emotionally intimate human-device relations underscore a potential for changing perceptions of companionship, of body, self, identity and lived experience.
Focus area: Assistive robotics and "smart" implants
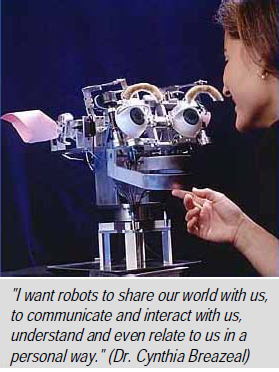 A policy perspective published by the European Commission (European Commission,
2008) states that "[t]omorrow's robots will not be confined to industry, but work in the
'real world', providing solutions for many societal issues".
Body/brain-device interfaces, including implants are also seen as important to the future of
individual and social well-being --in therapy, for security and modification purposes.
The interfaces are either invasive (implants) or non-invasive (e.g. scalp readings), and
designed to control the body, objects and devices and communicate with computer programmes.
Implants can also have embedded records, sensors, positioning and tracking devices.
A policy perspective published by the European Commission (European Commission,
2008) states that "[t]omorrow's robots will not be confined to industry, but work in the
'real world', providing solutions for many societal issues".
Body/brain-device interfaces, including implants are also seen as important to the future of
individual and social well-being --in therapy, for security and modification purposes.
The interfaces are either invasive (implants) or non-invasive (e.g. scalp readings), and
designed to control the body, objects and devices and communicate with computer programmes.
Implants can also have embedded records, sensors, positioning and tracking devices.These developments introduce a whole host of ESLA issues for reflection and debate, most of which turn on matters of human dignity and rights, social-cultural chance, politics of innovation and adequate legal frameworks.
Also prepared and delivered by Cesagen:
1) The Automata, the human machine and human-robot relations
Lecture at the ICTethics Summer School in Budapest Jun 2011.
2) On the interface of brains/bodies and devices
Lecture at the ICTethics Summer School in Budapest Jun 2011.
3) Cesagen (2012). Response to the Nuffield Council on Bioethics consultation on neurotechnology. Novel neurotechnologies: Intervening in the brain. Prepared by Gunnarsdóttir, K. with input from Chadwick, R., Hughes, J., Lewis, J., O'Connor, A. and Stephens, N.
4) "Smart" implants: therapeutic solutions, security and human enhancement - ICTethics Master Classes at the Wellcome Collection Conference Centre in London Oct 2011.
5) Gunnarsdóttir, K. (ed) (2010). The Convergence of the Physical, Mental and Virtual. A special issue in Studies in Ethics, Law, and Technology 4(3). Draft copy of the Editorial (Dec 2010).
-
The internet of things
The internet of things is a vision of both mundane and specialised objects being fitted onto a network or infrastructure, interconnected to exchange information, sensory data and share data-handling capabilities.
The concept suggests a radical extension of the internet as we know it and significant changes in what counts as a 'thing'. For example, the use of microchips with RFID, biosensors and positioning devices for implantation, effectively turn bodies and persons into networked things.
Focus area: Radio-frequency identification (RFID)
 An entire medical record, criminal record and other data on an individual or an object can
be stored on RFID devices and read from embedded chips. A global positioning device can
also be embedded in order to track objects, criminals, patients with Alzheimer's
disease, children and teenagers. It can be put to use by means of a Wide Area Network or even via
cell phone network. There are serious human dignity issues when the technology is developed
for security or commercial purposes with unprecedented intrusion into private affairs,
invasion into bodies and lack of clarity on reversibility in case there are serious operational
or governance challenges, health and security risks.
An entire medical record, criminal record and other data on an individual or an object can
be stored on RFID devices and read from embedded chips. A global positioning device can
also be embedded in order to track objects, criminals, patients with Alzheimer's
disease, children and teenagers. It can be put to use by means of a Wide Area Network or even via
cell phone network. There are serious human dignity issues when the technology is developed
for security or commercial purposes with unprecedented intrusion into private affairs,
invasion into bodies and lack of clarity on reversibility in case there are serious operational
or governance challenges, health and security risks.
-
ICT for human security
According to industry pundits, advanced ICTs are crucial to improve security. Accordingly, the official argument has been that public, private and corporate agencies need the new technologies to support, oversee and protect Western freedoms, transnational market democracy and, more generally, 'our way of life'.
Decisions on the uses of ICTs for human security reflect on ethical questions of purpose or mission, how to adequately protect data on persons and property, and ensure fairness in the treatment of suspects and all other persons.
Focus area: Biometric identification
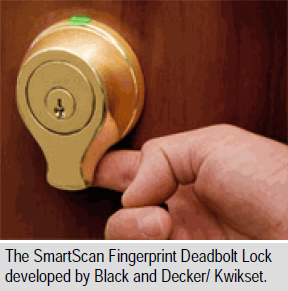 Questioning the assumptions on which 'security' already rests, opens the door to
alternative ways of framing what the problems might be and, consequently, which issues
need discussing and debating. The vast distribution of ICTs for surveillance and security
purposes, and the pivotal role given to biometrics, legitimises the involvement of publics
beyond the official institutional protocols for public engagement. The doors could be
opened to alternative views which already are struggling to find legitimacy using the
conventional engagement methods.
Questioning the assumptions on which 'security' already rests, opens the door to
alternative ways of framing what the problems might be and, consequently, which issues
need discussing and debating. The vast distribution of ICTs for surveillance and security
purposes, and the pivotal role given to biometrics, legitimises the involvement of publics
beyond the official institutional protocols for public engagement. The doors could be
opened to alternative views which already are struggling to find legitimacy using the
conventional engagement methods.
-
Issues in Focus
This list of Issues in Focus was defined during the design-stage of the ICTethics project so it is presented here in the original order. Other related and overlapping issues have emerged during the course of the project and are dealt with as needed across all the research and summary notes.













